什么是HSTS?为什么它在网站中很重要?
articles
8pa1blOb37PWea5wdMQzOr2tUdOFbJwehkK2j6OH6BPrG6st
Language/语言:
English
简体中文
作者: Ken Deng
发布于2021年8月22日
本文大约3200字,阅读需要14分钟
你好!我叫Ken,我是一名A Level高中生。欢迎来到Ken的学习之旅计算机知识解析!
最近,为了提升网站的安全性,我的网站已启用HSTS安全协议。虽然HTTPS非常重要,但在从HTTP跳转到HTTPS的过程中也是有危险的。
我们在IGCSE (0478)和A Level (9618, 9608)的计算机当中会学到HTTPS、SSL和TLS安全传输协议,但HSTS这个知识点没有涵盖在这些课程大纲和考纲当中,它只是一个扩展的知识点。
百度、谷歌、YouTube、剑桥大学、牛津大学等网站已经启用了HSTS,因此人们可以安全地浏览互联网。
这是我新网站中的首个知识解析。从现在起,我将会在发布我优秀的学习方法的基础上,同时发布详细、易懂的数学 (CAIE国际课程学科代码:0580, 0606, 9709, 9231)、物理 (0625, 9702)、化学 (0620, 9701) 和计算机 (0478, 9618, 9608) 的知识解析。
你知道HSTS是怎么进一步提高用户访问网站的安全性,以及为什么会这样吗?让我们开始吧!
什么是HSTS?
HSTS是HTTP Strict Transport Security的缩写,它是进一步保证访客安全的保护层。
现在,越来越多的网站已经开始使用HTTPS安全加密传输协议,特别是银行、订票和购物网站,黑客无法看懂和更改加密后的信息。HTTPS使用了安全证书、加密算法和密钥。
在生活中发现学科知识 - 2019年首创的学习方法
在生活中发现🔍、应用🔬和分享📤学科知识可以帮助自己牢记知识点、教别人、解释生活中的现象。
这是我在2019年(初中)发明、首创🌟的学习方法。当时仅在朋友圈(朋友、同学之间)可见。
在2021年,我开始在文章📄的绿框中插入、分享发现的学科知识(可以是初中、高中或大学的知识)。
现在,我将插播一个IGCSE计算机(0478)的知识:SSL和TLS
SSL是Secure Socket Layer的缩写,它是一个安全协议,TLS是Transport Layer Security的缩写,它是SSL的升级版,它比SSL更加安全、高效。
浏览器收到DNS域名服务器回复的服务器IP地址后,有着几个步骤来建立安全连接:
- 浏览器向服务器发送请求,让服务器识别自己,并选择合适的SSL/TLS的版本和加密算法;
- 服务器向浏览器发送它SSL安全证书的副本,以及它的公钥;
- 浏览器与证书颁发机构(CA)验证证书;
- 如果证书有效,浏览器会向服务器发送请求,并建立私钥和会话,否则浏览器会阻断网站的访问;
- 服务器将开始数据的传输
TLS有着两个协议:握手协议和记录协议。握手协议用来建立安全连接,记录协议可以在有或没有加密的情况下使用。
普通用户并不知道HTTP、HTTPS、SSL等计算机术语,因此他们通常会在没有输入“https://”前缀的情况下,直接输入网址。HSTS是保证访客安全的保护层。有时,黑客会在网站从HTTP跳转到HTTPS的过程中修改数据,这样是很不安全的,但HSTS可以在你没有在地址栏中输入“https://”的情况下,强制让浏览器内部(浏览器内,不请求服务器)跳转到HTTPS。只要访问过我的网站,之后浏览器都会自动跳转到HTTPS。
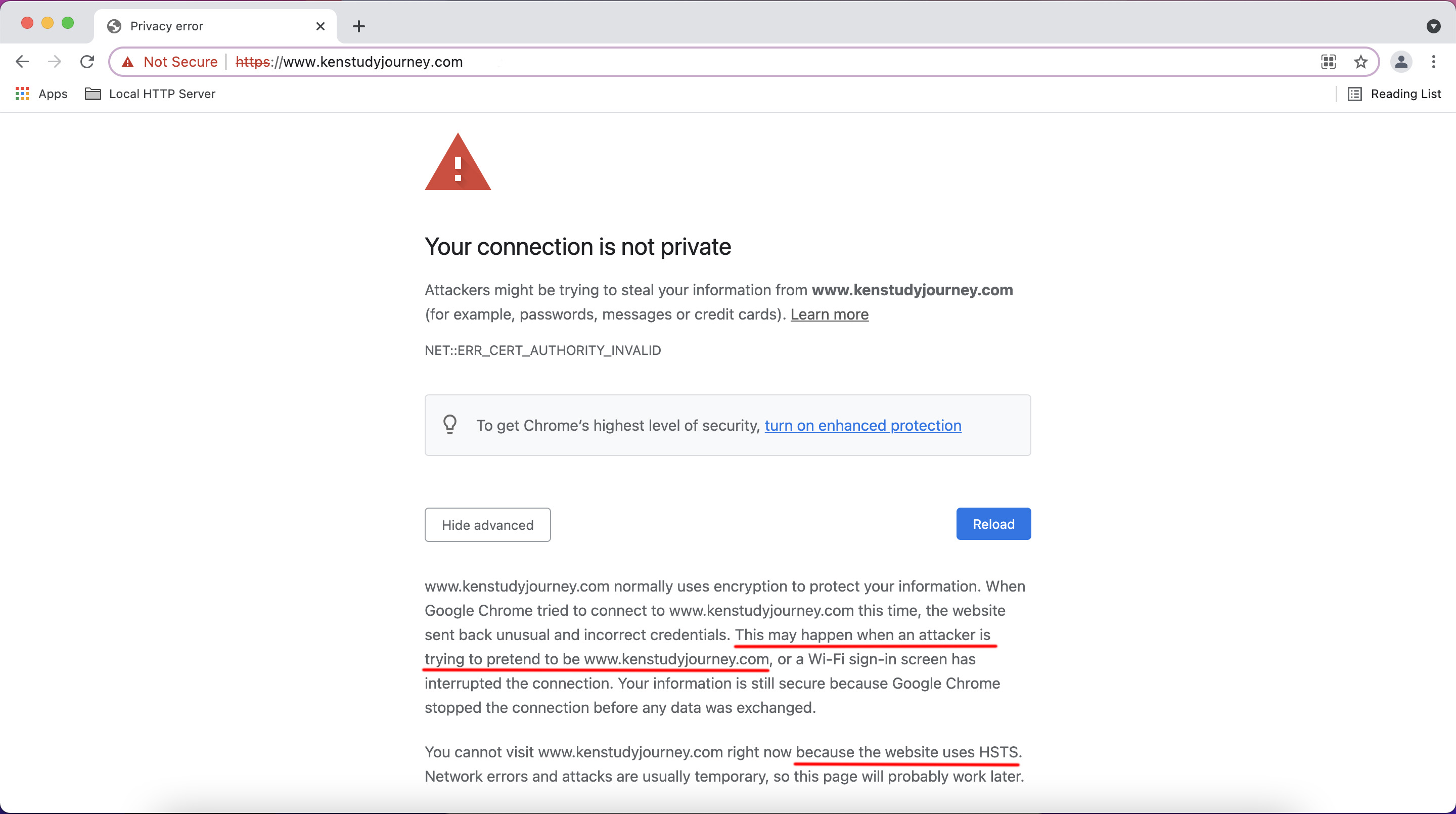
如果有黑客在中间破坏HSTS的安全传输过程,浏览器便会阻断网站的访问,就像这个界面:
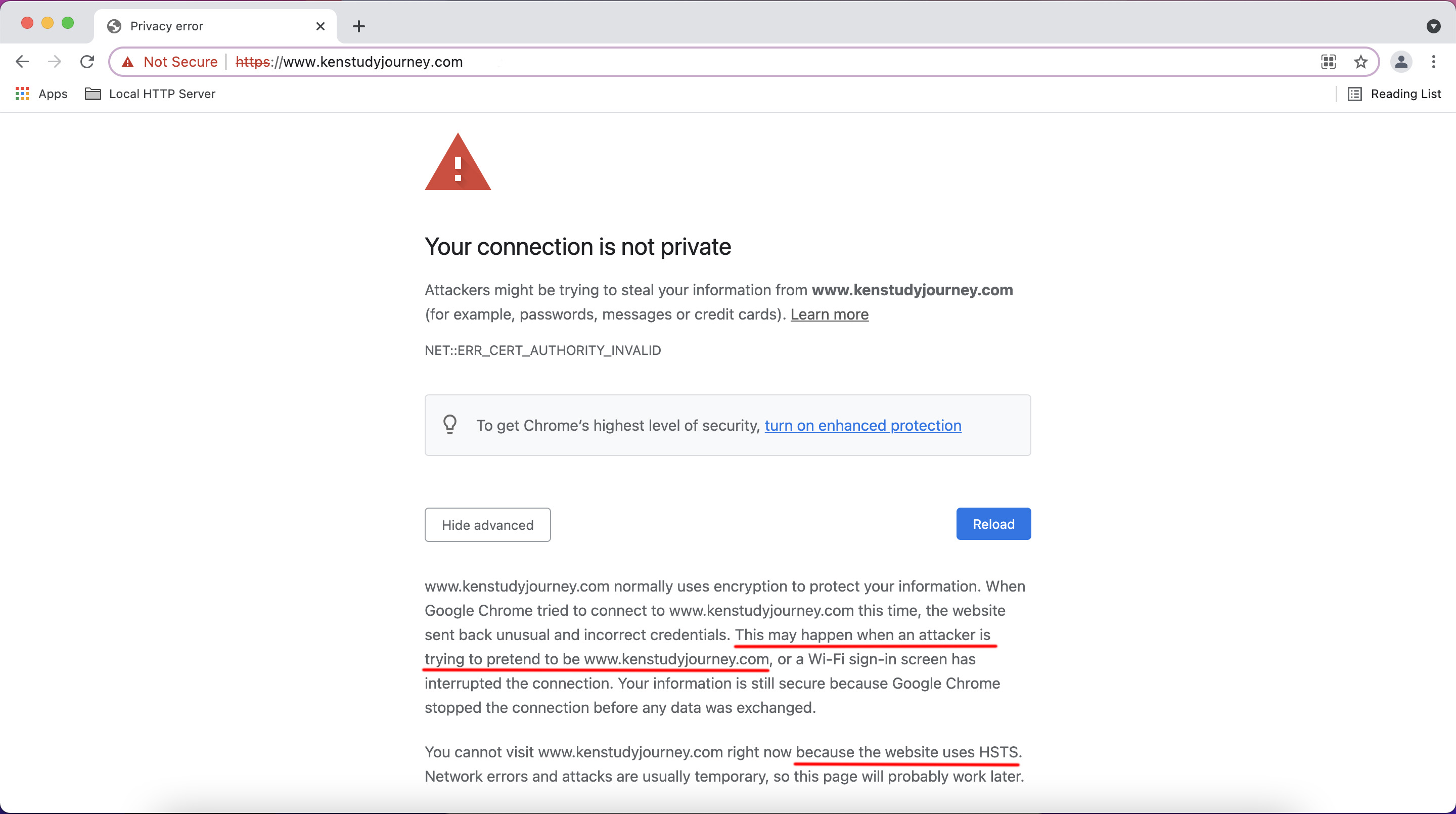
图片中显示的内容是:
攻击者可能会试图从www.kenstudyjourney.com窃取您的信息(例如:密码、通讯内容或信用卡信息)。了解更多信息
www.kenstudyjourney.com通常会使用加密技术来保护您的信息。Google Chrome此次尝试连接到www.kenstudyjourney.com时,此网站发回了异常的错误凭据。这可能是因为有攻击者在试图冒充www.kenstudyjourney.com,或Wi-Fi登录屏幕中断了此次连接。请放心,您的信息仍然是安全的,因为Google Chrome尚末进行任何数据交换便停止了连接。
您目前无法访问www.kenstudyjourney.com,因为此网站使用了HSTS。网络错误和攻击通常是暂时的,因此,此网页稍后可能会恢复正常。
HSTS和WiFi登录认证页面之间的冲突
但需要注意的是,如果你正在使用公共WiFi,它可能会跳转到登录认证的页面,出现该错误是正常现象。WiFi路由器之所以可以让浏览器跳转到登录页面,是因为它可以更改不安全的HTTP连接中的数据。在登录WiFi之前,所有HTTPS网站都是无法访问的。
随着HTTPS和HSTS的发展,再寻找没有HSTS、允许HTTP连接的网站是很难的。
苹果、微软和我提供了测试页面,测试WiFi是否包含登录页面,它们可以被HTTP访问,你可以在浏览器中输入 http://captive.apple.com或http://www.msftncsi.com进行测试。正常情况下会显示Success,公共WiFi会跳转到登录页面。
新的iPhone、iPad和MacBook通常会在WiFi连接成功后访问captive.apple.com,因此它们可以自动弹出登录认证页面。
除了带有登录认证页面的公共网络以外,访问我的网站时,如果出现了上图中的界面,不要惊慌,也先不要访问我的网站。你可以更换WiFi,也可以使用手机流量(3G、4G或5G)。
有些网站即使启用了HTTPS和安装了SSL安全证书,程序员却没有或忘记增加自动跳转到HTTPS的功能。这就意味着,如果我们没有在网址前面加上前缀"https://",浏览器将不会使用HTTPS安全传输协议。
我顺便给你一条建议,你在访问一个网站时,最好在网址前面加上"https://"前缀,只有浏览器显示HTTPS错误页面时(即无法安全连接服务器,也就是网站没有启用HTTPS,没有安装SSL证书),才去掉这个前缀,或者改回"http://"。
比如说,访问百度时,你可以输入https://www.baidu.com
HSTS响应头
当你访问带有HSTS的网站时,服务器会发送如下响应头,它会像Cookie一样保存在浏览器中。它的意思是,在接下来的180天(15552000秒)内,该浏览器必须以HTTPS安全协议访问本网站。
Strict-Transport-Security: max-age=15552000
网站的管理员或程序员可以修改HSTS的持续时间,为了安全起见,建议将时间设置为180天(半年)以上。
HSTS可以自动续期,每次访问我的网站时,服务器都会发送一次HSTS响应头。第二天再访问我的网站时,过期时间将会变为接下来的180天。
2020年,当我在旧网站中使用WordPress框架时,并没有打算启用HSTS,因为我很担心如果网络出现错误,或者网站SSL证书出现了错误,将无法访问网站。
HSTS预加载
Cloudflare等网站启用了一个HSTS的特殊功能:HSTS预加载。
我们知道,首次访问网站,没有加"https://"前缀是不安全的。在访问网站之前,浏览器是没有保存HSTS响应头的,因此从HTTP跳转到HTTPS的过程可能会有危险。
然而,HSTS预加载功能解决了这个问题,新版的浏览器都有自己的预加载清单。即使你没有访问过某个网站,它也会强制使用HTTPS。
看看这个响应头,它与上面我提到的响应头有着一些不同之处。
Strict-Transport-Security: max-age=31536000; includeSubDomains; preload
要加入主流浏览器的HSTS预加载列表,首先网站必须要满足以下要求:
- 网站必须安装有效的SSL安全证书
- 持续时间必须为一年以上(365天,31536000秒)
- HSTS响应头必须包含子域名,比如说planner.kenstudyjourney.com是kenstudyjourney.com的子域名
- 所有子域名都必须启用HTTPS、自动跳转和HSTS响应头
- 响应头必须包含“preload”属性,它会告诉浏览器,该网站想要加入预加载的列表中
如果网站连续几个月满足了这些要求,域名将被自动加入到预加载的列表中。
HTTPS浏览器内部跳转
现在,我将介绍浏览器内部跳转HTTPS功能的工作原理,了解HSTS是如何实现浏览器内部跳转的。
内部跳转可以防止在公共WiFi下,跳转到HTTPS过程中被黑客跳转到其它网站上的情况。
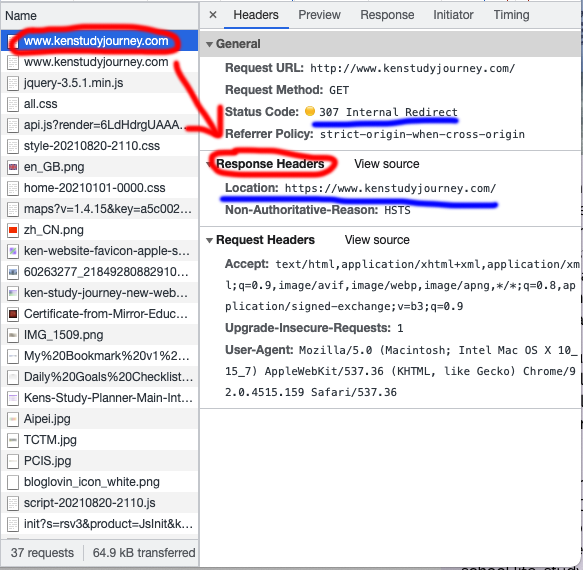
比如说,在家里使用不安全的HTTP协议,第一次访问网站时(http://www.kenstudyjourney.com),浏览器会收到下列响应头。
HTTP/1.1 301 Moved Permanently
Location: https://www.kenstudyjourney.com
HTTP状态码分为了很多种,它会表示服务器的状况,并且它是由浏览器来处理的。下面我给大家介绍一些常见的HTTP状态码:
- 200 OK (网页正常)
- 301 Moved Permanently (需要跳转到其它URL链接)
- 400 Bad Request (没有按要求向服务器中发送请求)
- 403 Forbidden (服务器拒绝访问,比如说服务器阻止IP地址、国家/地区时会见到)
- 404 Not Found (最常见的状态码,表示请求的资源在服务器中找不到)
- 429 Too Many Requests (短时间内请求次数过多,超出了网站管理员设置的“频次限制”)
- 500 Internal Server Error (服务器后端代码报错,出现了bug,无法执行)
- 503 Service Unavailable (服务器过载,或者网站正在升级维护)
你可以看到,它接下来会跳转到我HTTPS版本的网站。
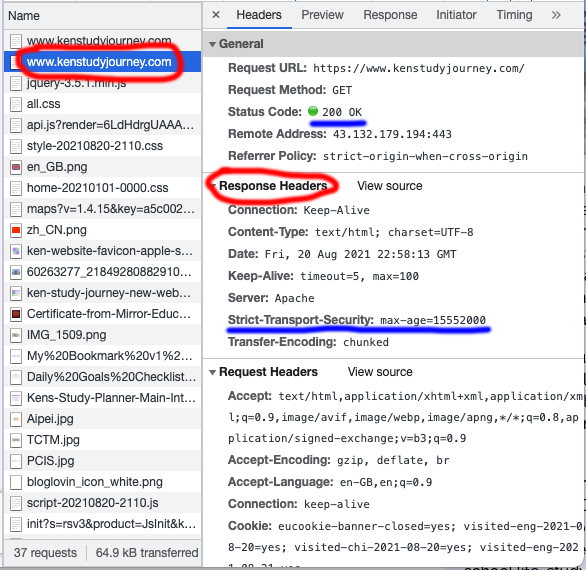
当浏览器访问我的HTTPS网站时,它会收到下列响应头,以及网站的内容。
HTTP/1.1 200 OK
Strict-Transport-Security: max-age=15552000
当浏览器收到HSTS响应头后,它会存到浏览器的缓存中。
现在,假如你连上了公共WiFi,并再次访问我的HTTP网站时,响应头是不一样的。
HTTP/1.1 307 Internal Redirect
Location: https://www.kenstudyjourney.com
那么为什么会这样呢?这是因为浏览器存储了HSTS协议要求,整个过程只会花费2毫秒,并且浏览器不会在跳转到HTTPS的过程中,将请求发到我的服务器上。我将会在下一个部分告诉你查看服务器响应头的方法,如果你感兴趣,你可以进行查看。
这就是为什么HSTS在网站上是非常重要的,它可以将网站跳转到HTTPS,而不用请求服务器。
查看响应头
在Chrome、Firefox、Microsoft Edge等浏览器中(Safari除外),都有着开发者工具,它可以查看网页的代码、请求头和响应头。程序员们会利用这些信息来调试网站。
现在,我将会教你如何在浏览器中查看网站的响应头,包括跳转信息和HSTS信息。
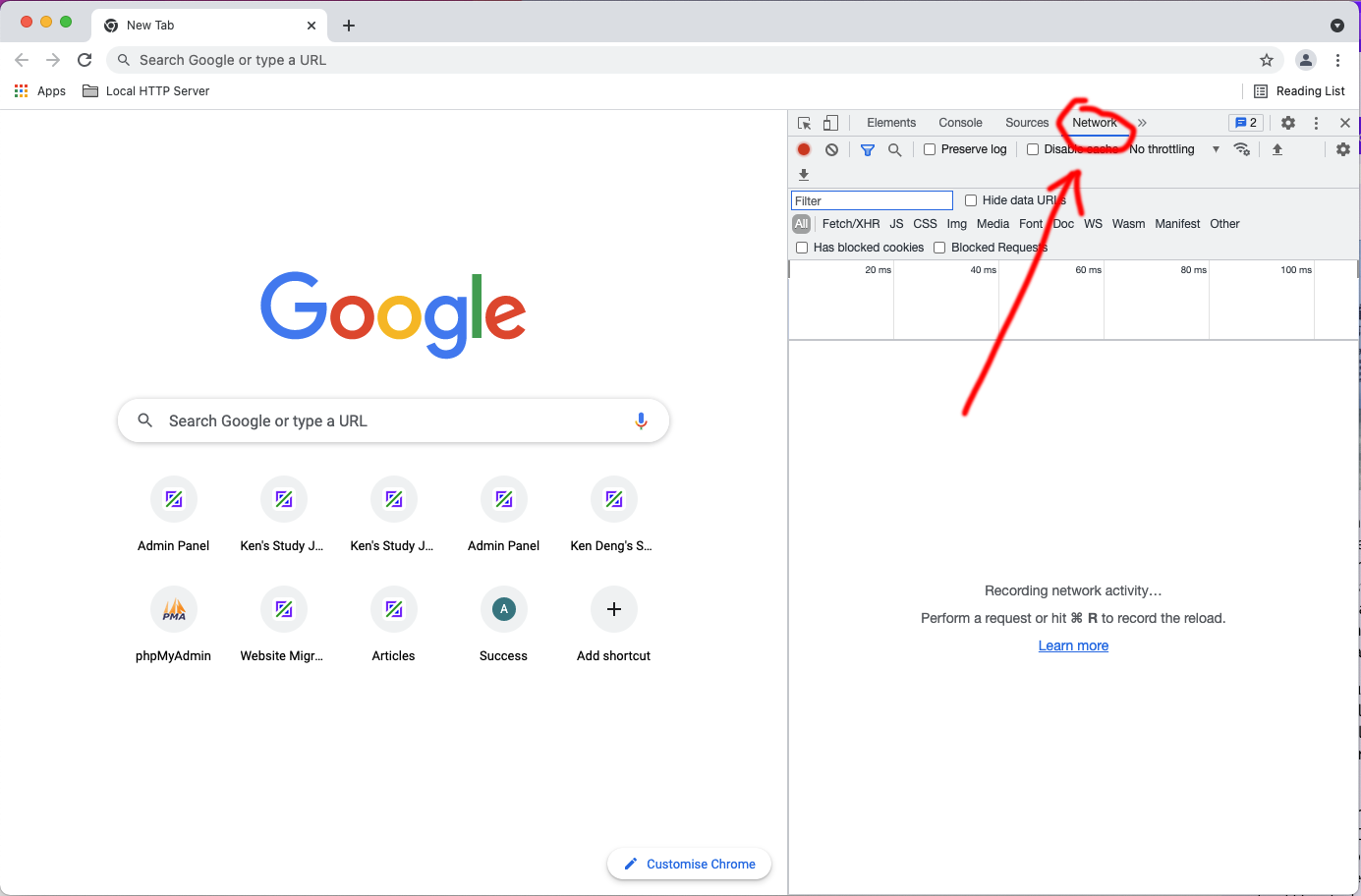
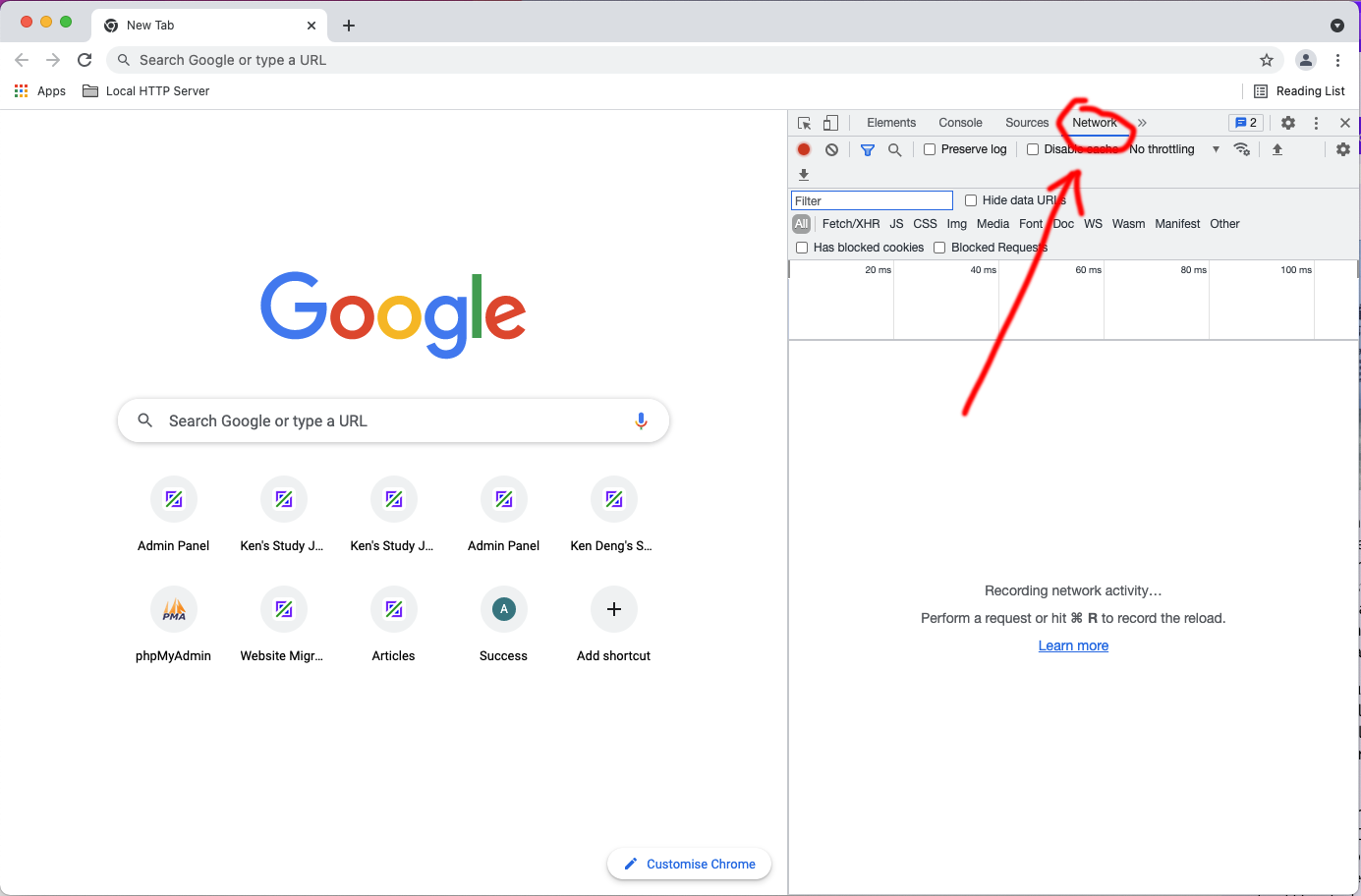
首先,打开浏览器,在访问网站之前,按F12或option+command+I打开开发者工具,并点击Network。
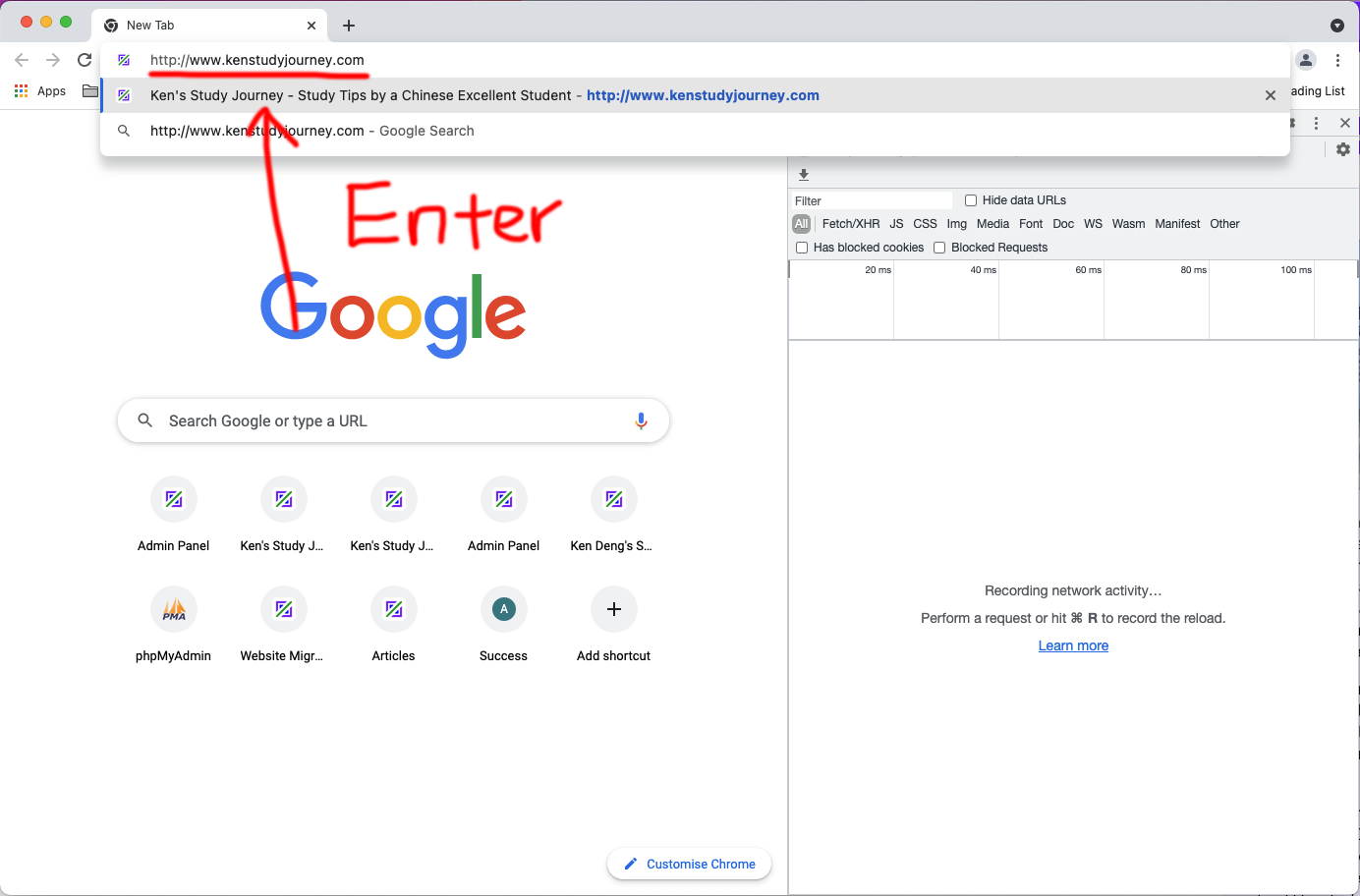
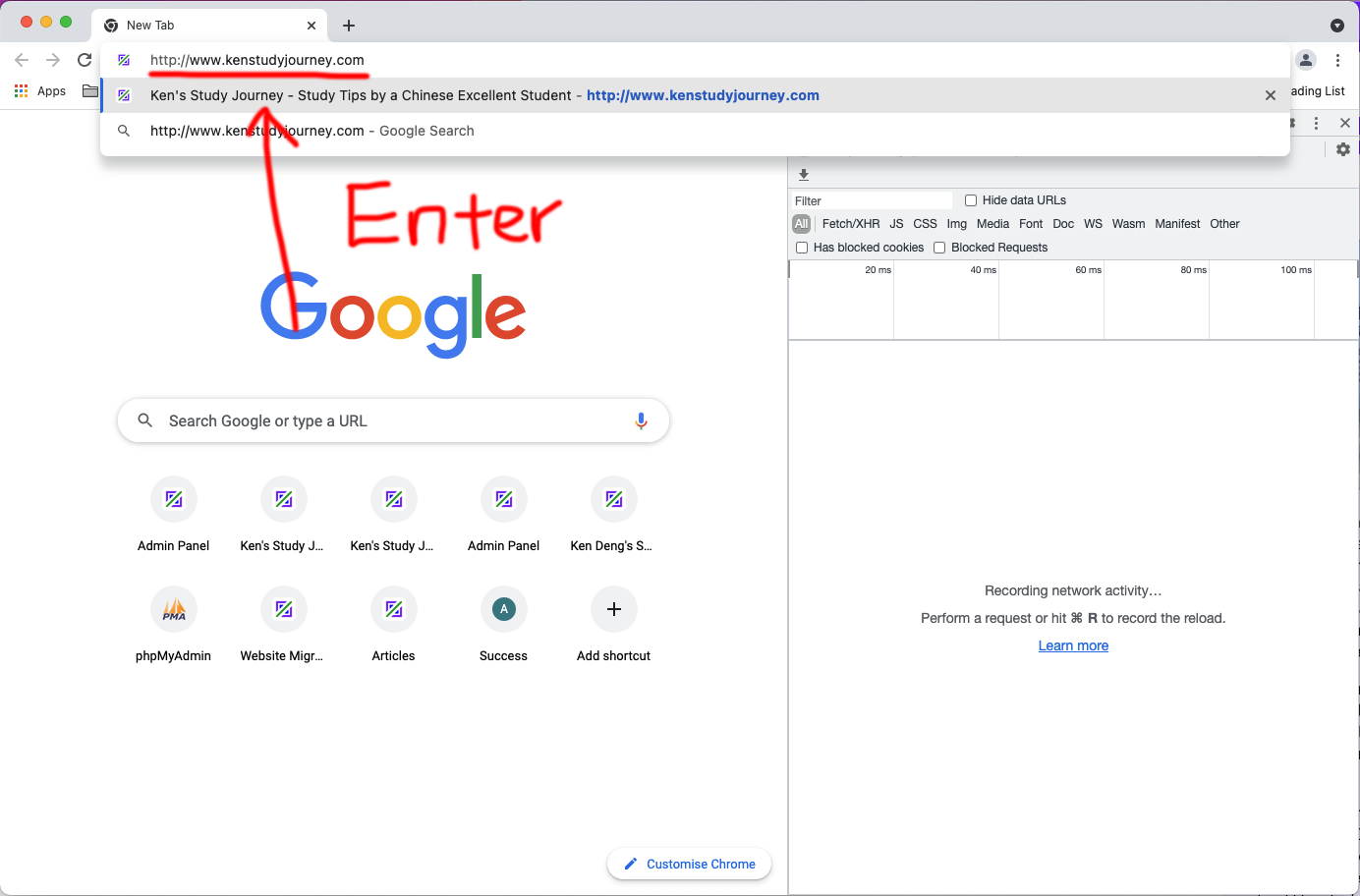
随后在地址栏中输入要测试的网址。
出现文件列表后,滚动到顶部,点击第一个文件(或者与网址有直接关联的文件),你可以看到有307内部跳转或301跳转的状态码(注:跳转可以是301,也可以是302)。在状态码的下面,可以看到Location显示着要跳转的网址。
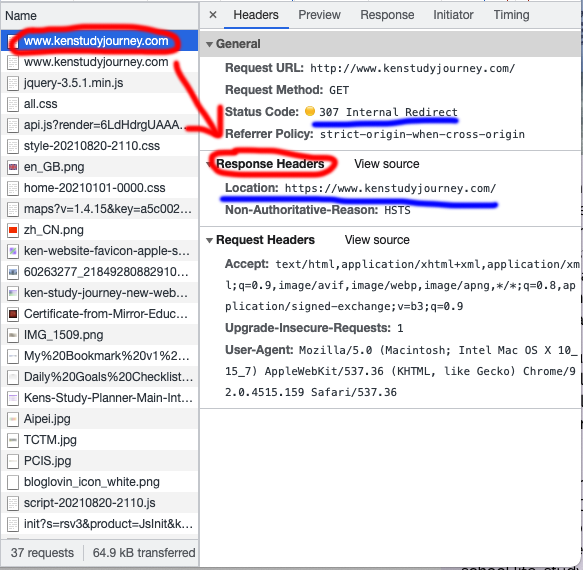
点击第二个文件,它将显示200 OK的状态码,以及带有有效期(max-age)的HSTS要求。
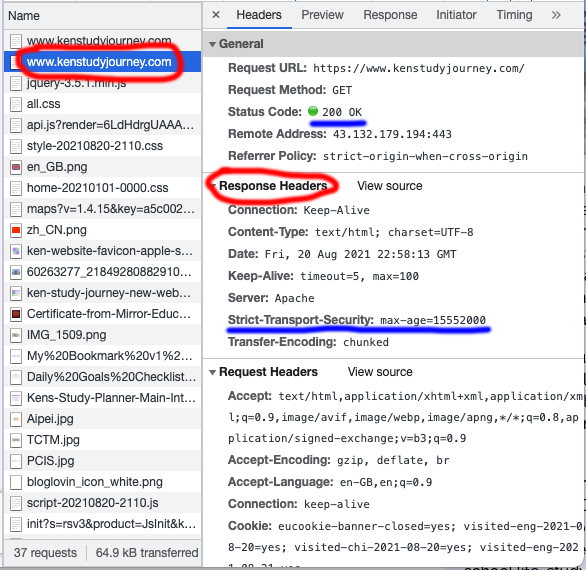
如果你看到了"Strict-Transport-Security",说明网站开启了HSTS,max-age的值表示HSTS的有效期(秒数)。
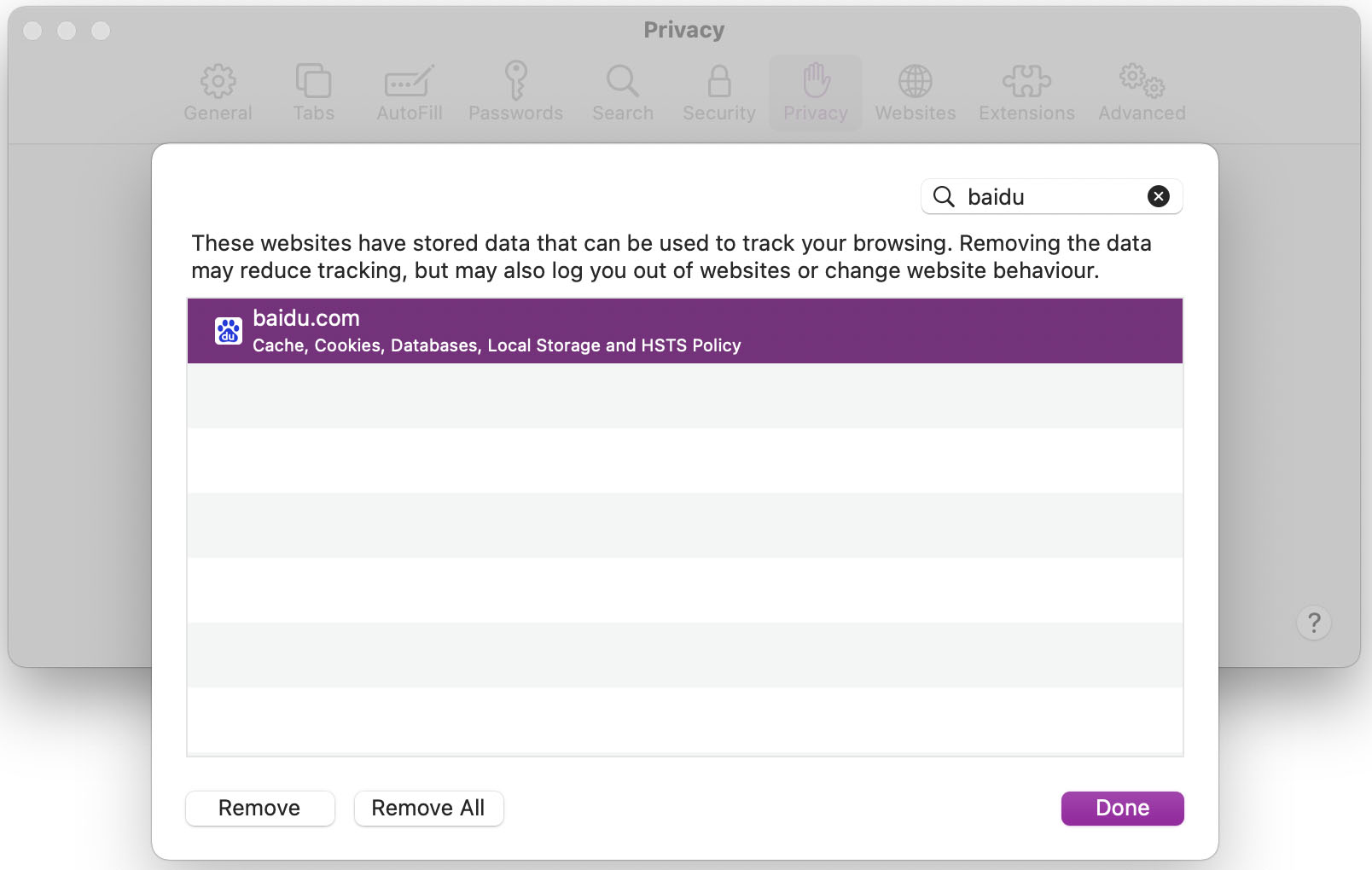
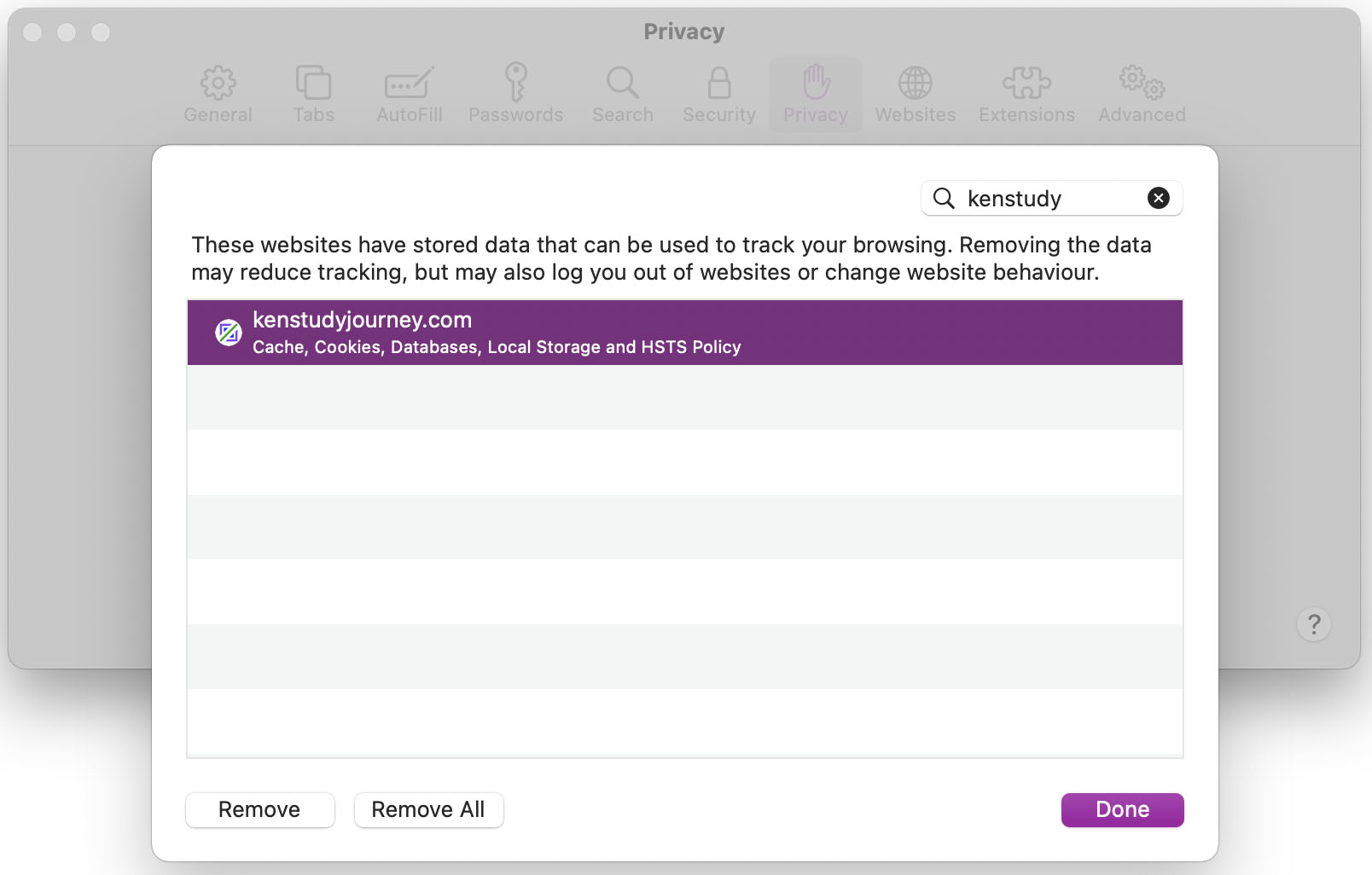
在Safari中查看HSTS
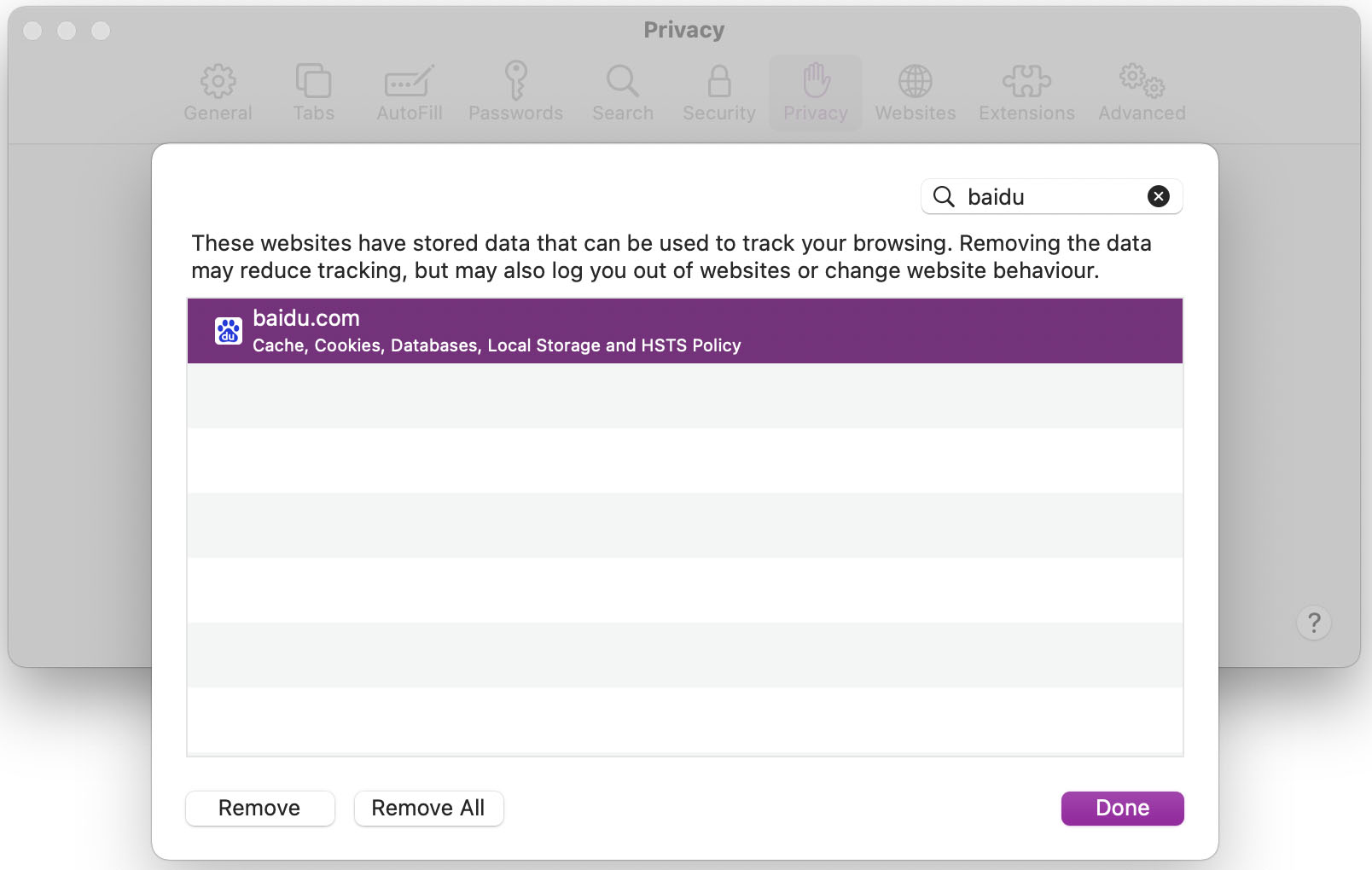
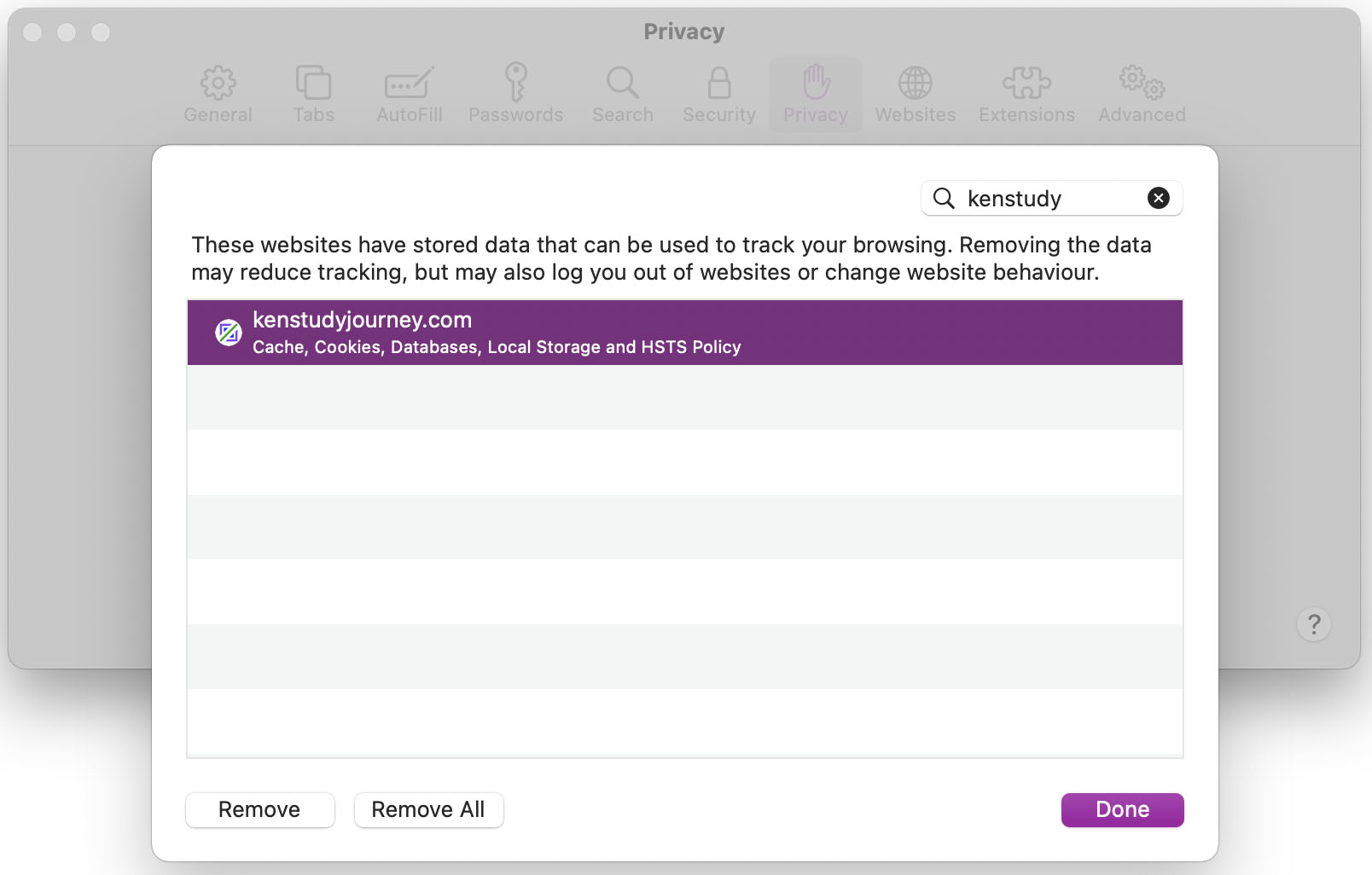
如果你用的是Safari,它有另外一种方法来查看网站是否开启了HSTS。
首先,访问相应的网站,浏览器会接收并保存HSTS响应头。
然后打开偏好设置,并点击隐私-管理网站数据,搜索相应的域名。如果它启用了HSTS,它将会有HSTS的显示。
查看HTTPS安全等级
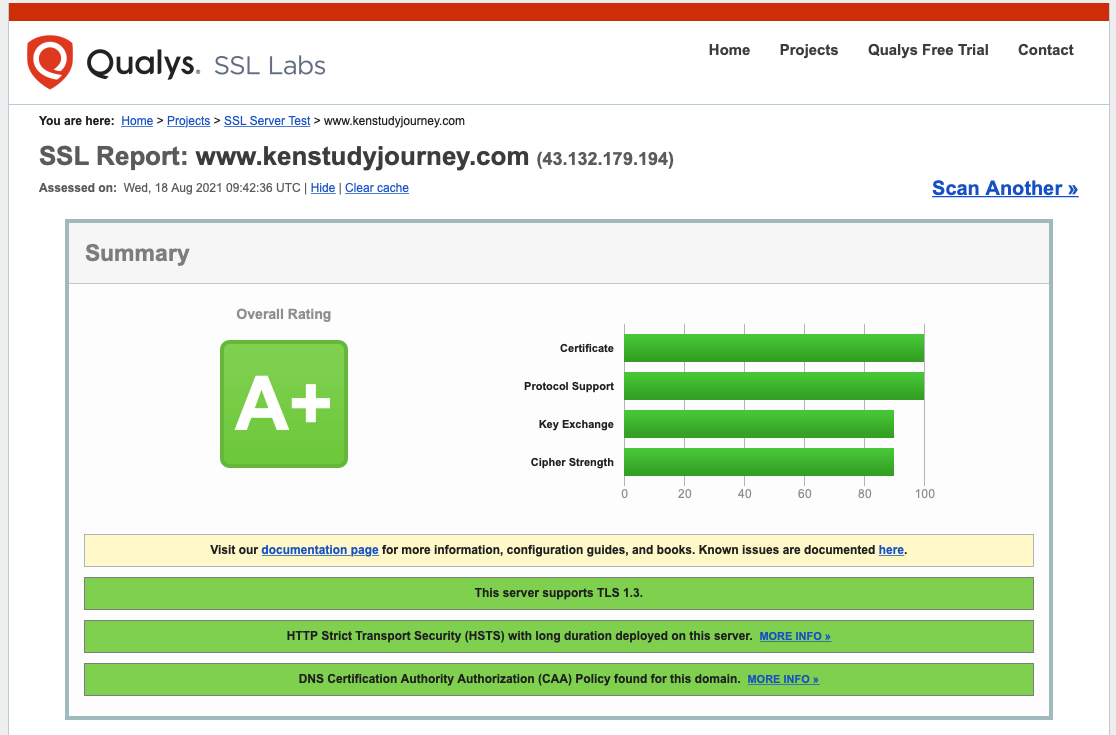
世界上有着一个能够查看网站安全等级的工具,它就是SSL Labs,它由Qualys提供。
它会检查网站是否含有有效的SSL安全证书、正确和安全的连接协议(TLS和SSL),以及是否开启HSTS。
它的等级与剑桥CAIE国际课程考试的等级极为相似(A+ (A*)、A、B、C、D、E、F、T (U))。
我的网站之所以得到了A+(我会把它看成A*,因为我正在学习剑桥IGCSE和AS、A Level国际课程),是因为它使用了安全的协议,以及开启了HSTS,这就意味着同学们可以安全地在我的网站中学习知识,不受黑客的侵害。
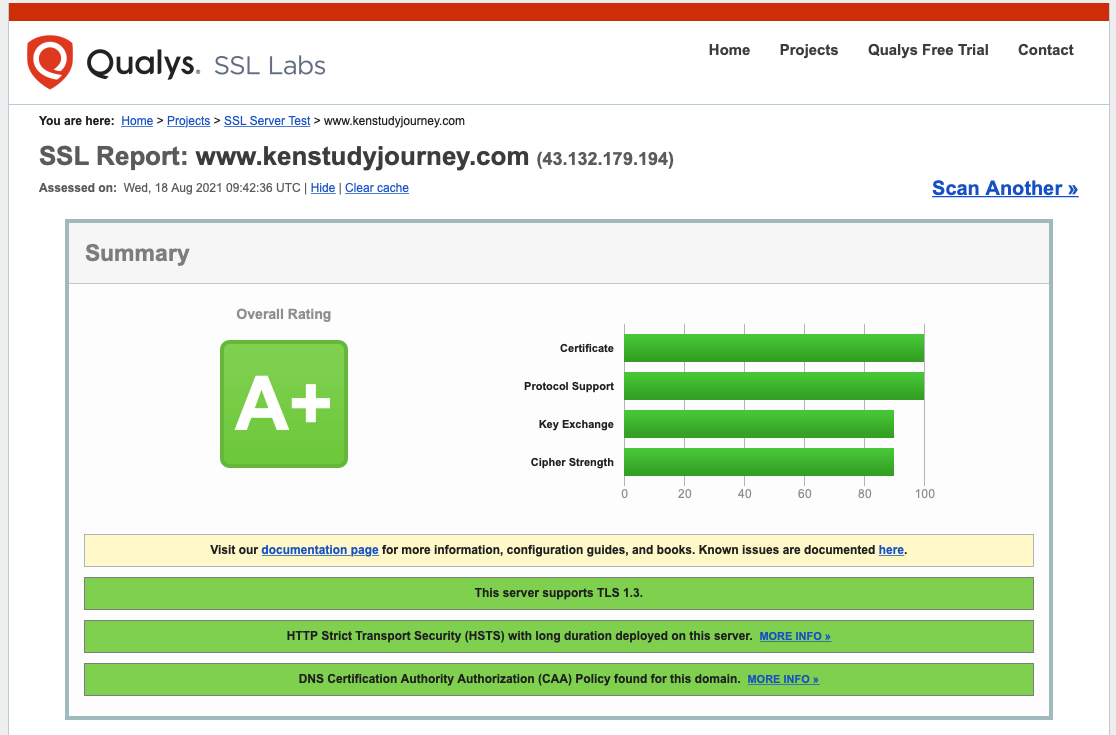
如果你的网站想到得到A+的等级,需要满足以下要求:
- 安装了有效的SSL证书(可以是免费的Let's Encrypt);
- 证书需要有较强的加密性(密钥交换至少1024位);
- 禁用了旧版的TLS和所有SSL(SSL2.0、SSL3.0、TLS1.0、TLS1.1),使用旧版的SSL可能会受到PODDLE攻击,它与关闭旧版的2G和3G网络的原理相似;
- 开启了HSTS(至少180天);
- 使用了较新的加密套件;
总结
HSTS是一个可以在用户的浏览器中存储的记录,它可以防止从HTTP跳转到HTTPS过程中的攻击,因此它可以进一步提高网站的安全性。
本篇关于HSTS安全协议的知识解析已结束,感谢你的阅读。
订阅我的最新消息邮件,获取我最新的文章、新闻、学习方法、教程、生活中的实用知识等内容。
如果你喜欢这篇文章,请在下方点击点赞按钮,并分享这篇文章。如果你有任何想法,你也可以在下方留下评论。这是我的第一篇学科知识解析,难免会存在错误。如果你发现了错误,你可以联系我进行更正。
有问题或看不懂文章内容吗?请及时联系我,我将会很乐意帮助你。我说英语和中文。




你的评论发送成功,但为了防止垃圾和负面评论,它需要经过我本人的人工审核,才能显示在网站中。
请耐心等待几天,当评论审核通过并被回复时,你将会收到一封邮件。